This document outlines the University approved process for securely encrypting Personally Identifiable Information (PII).
Prerequisite
7Zip software needs to be installed on the end user’s computer. Please contact the SAMI Support Desk to request the installation of this software. If justification is needed, notify the service desk that 7Zip is needed to encrypt documents containing PII.
Process
Encrypting Files and Folders
To encrypt a single file, find the file in your directory (or where you have it saved).
- Right click on the document (do not open the document)
- On the drop down menu, Find 7zip
- Click “Add to archive…“
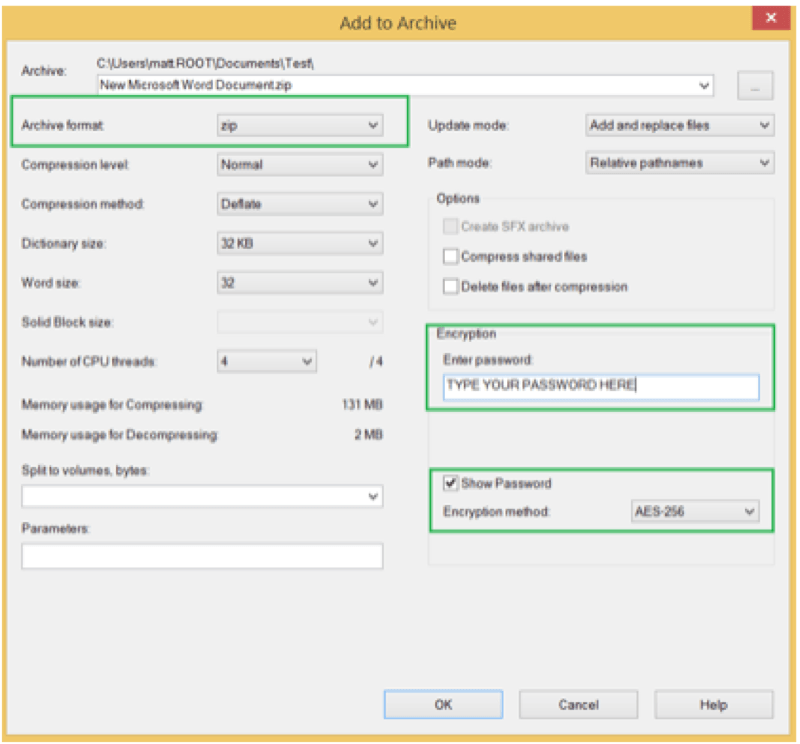
- When 7zip opens, there are three (3) settings which need to be changed:
- Archive Format = Select zip from drop down
- Encryption Method = select AES-256 from drop down
- Check “show password” and type in a password that the user creates
- Click “OK“
- A 7Zip Archive with the encrypted document will now appear in your directory
NOTE: Do not utilize any password that you use to access internal systems. The password cannot be recovered if forgotten.
Editing Encrypted Files and Folders
When editing an encrypted file or folder, you must make sure that you leave the 7zip archive open. If you close the archive, you will be able to work on the document, but it will not save.
Opening an Encrypted File or Folder
To open an encrypted file or folder:
- Right click on the 7Zip archive
- On the drop down menu, find 7Zip
- Click on the first “Open archive”
- Click to open your document
Saving an Encrypted File or Folder
To save an encrypted file or folder:
- Save the document as normal
- Upon closing document, the 7Zip archive will prompt the user to save the changes